Attackers abuse the Universal Plug and Play (UPnP) protocol that comes with routers and uses the devices to create a powerful proxy network to effectively hide the origin location of the traffic origin.
It appears attackers used this multi-purpose proxy botnet to launch various attacks such as DDoS, Account take over, Credit Card Fraud, Click Fraud, Spamming, and Phishing.
UPnP is a service that makes’s the connectivity ease, it allows devices to expose connection and service automatically to other devices connected to the local network.
Akamai published the report on how the UPnP-enabled devices detected as participants in attacks, “we discovered that some devices appeared to be more susceptible to this vulnerability than others, and contained malicious NAT injections”.
How Attackers leverage UPnP Vulnerability
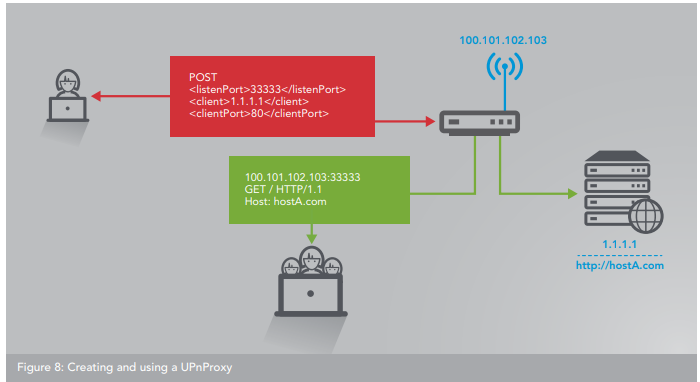
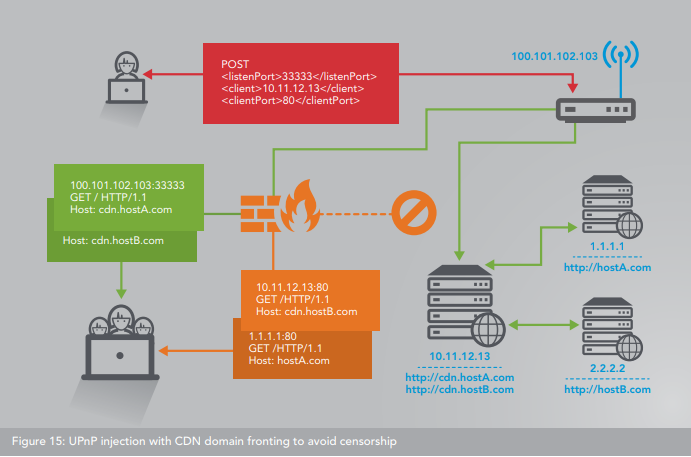
Attackers obtain required information to connect with TCP-enabled UPnP daemon through SSDP probe response and by modifying local IP address to public IP address allows the attacker to establish the connection with UPnP daemon.
Now hackers can inject bypassing local firewall to access the access the Internal IP address beyond the router or pointing the router itself to the IP or domain that presented outside of the LAN network.

According to Akamai report “In initial Internet-wide scans, over 4.8 million devices were found to be vulnerable to simple UDP SSDP (the UDP portion of UPnP) inquiries. Of these, roughly 765,000 (16% of total) of the identified devices were confirmed to also expose their vulnerable TCP implementations. Over 65,000 (9% of vulnerable, 1.3% of total) of these vulnerable devices were discovered to have NAT injections”.
By having a widely distributed Multilayer proxy network that comprises encrypted and millions of unique IP address around the world the botnet authors post a tremendous challenge for investigations.

Researchers said there is no easy way for a human to audit or modify them on the devices themselves and the best way is to audit your NAT table entries.
A wide range of the devices affected by this vulnerability that covers 73 brands/manufacturers and close to 400 models. The possible mitigation is to replace the device or to disable vulnerable UPnP services.