SOC First Defense – Understanding The Cyber Attack Chain – A Defense with/without SOC
This article will help you to understand the SOC modern cyber threats and the most commonly used attack surfaces behind any malware/cyber-attacks.Most times, cyber-attacks...
SOC Third Defense Phase – Understanding Your Organization Assets
In our first phase, we have seen the basic defense mechanisms which were recommended in organizations.In our second phase, we have seen the...
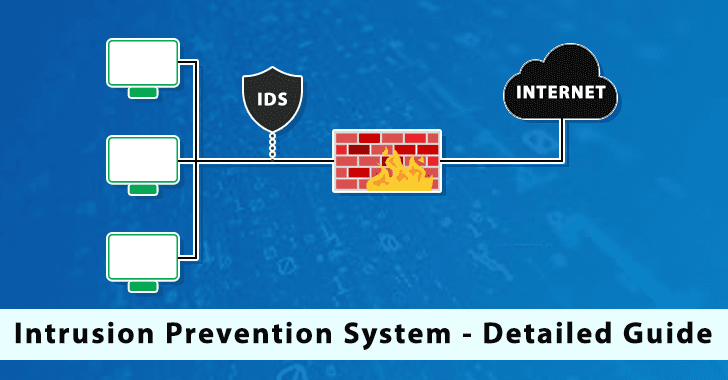
Intrusion Prevention System (IPS) In-depth Analysis – A Detailed Guide
Like an Intrusion detection system (IDS), an Intrusion prevention system (IPS) screens network traffic. In this article, we deep dive into Intrusion Prevention System...
Modern CyberSOC – A Brief Implementation Of Building a Cyber Security Infrastructure
In earlier years, everyone depends on CyberSOC (including firewalls, WAF, SIEM, etc.) and the priority in building the SOC provides security, and the CIA...
Pros and Cons of SOC – Outsourcing Concept
Security Operations Center (abbreviated SOC) — is a complex of specialists, processes, and technologies aimed at effective monitoring (detection) and response to information security...
Patch Manager Plus – A Complete Automated Patch Management Tool For Windows, Linux, Mac
Managing the organization’s critical patches to keep computers up to date is very hard since there are hundreds of products and software deployed within...
Diving Deeper Into Windows Event logs for Security Operation Center (SOC) – Guide
Cyber Security operations center is protecting organizations and the sensitive business data of customers.It ensures active monitoring of valuable assets of the business...
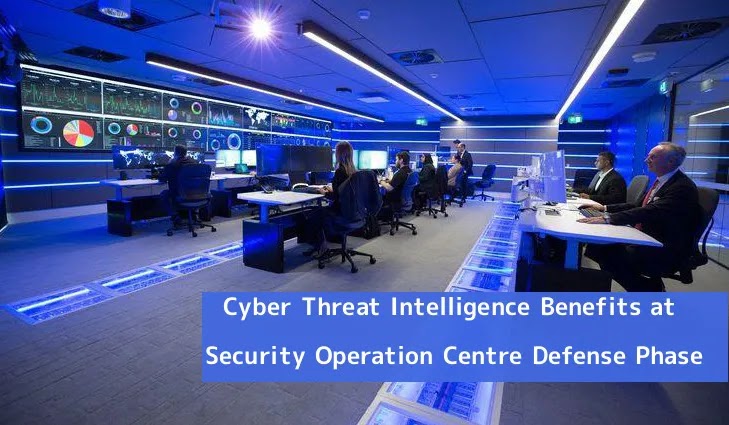
SOC Fourth Defense Phase – Cyber Threat Intelligence Guide
Cyber Threat intelligence is one of the most critical concerns in the evolving threat environment of rapid day-zero attacks, cyber-criminality and espionage activities; the...
How To Build Your Own SOC
Building a Security Operations Center (SOC) can be enormous, taking time and resources from your current IT department if not planned or strategized correctly.For...
Secure Your Network From Advanced Cyber Threats With Next Gen SIEM & Open XDR
Security information and event management, or SIEM, was introduced some 17 years ago. It makes sense for a next-gen SIEM to emerge now, or...











.png)
%20(1).jpg)